The Internet has many benefits and has made our lives easier in many ways. However, it also has a dark side and it is important to take measures to ensure that our information is secure at all times. Cybercriminals are constantly devising new techniques to get access to your financial details, passwords, and all the personal data that can be collected online.
You may not notice anything suspicious when you are connected to the Internet, but the truth is that malicious hackers are always lurking and ready to take your sensitive data.
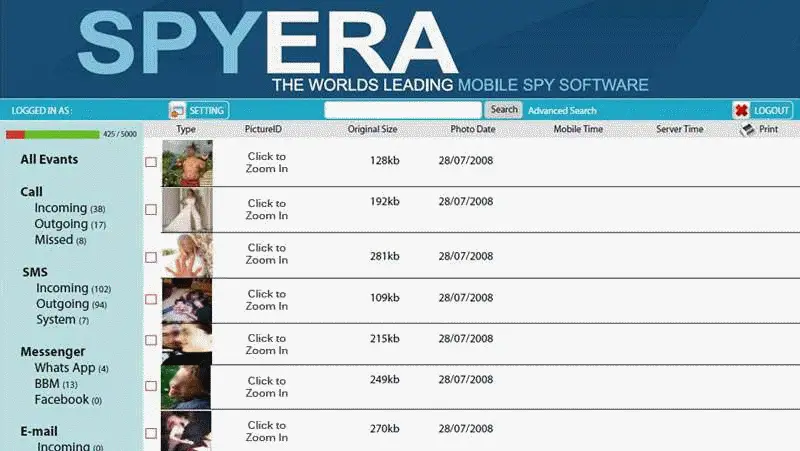
Unfortunately, technology is often used with illegal purposes and while online fraudsters have many new methods to prey on your information, keyloggers and software that can monitor keystrokes, are still very popular.
This technology has proven to be effective to steal information from unsuspecting victims, because it is very difficult to detect. The good news is that if you pay attention to the signs, you can avoid becoming a target of keyloggers.
There are certain things that will tell you if you are being monitored and we will share some tips to help you to identify the risk and avoid it. Here is what you need to keep in mind in order to maintain the security of your data.
Prevention is the best defense
One of the most basic steps to ensure that your information is not compromised, is to keep track of the programs you install. Make sure that you are familiar with your control panel and if you notice any unusual program, check it. You may come across hardware that your computer detects, even if it is not visible to you.
Scanning your computer regularly is another effective way to prevent security issues related to spyware. A reliable anti-virus can keep trojans at bay and detect any potential risk. It is also important to keep your firewall active all the time. Additionally, it is a good idea to check the task manager regularly (simply press control +alt + delete to open it) to monitor the running programs.
Don’t open any file from an unknown source and ignore any emails that request your login details and passwords, even if they seem to come from your bank, or an online service that you normally use. Fraudsters often use phishing emails to steal information. Usually, they pretend to be trusted companies and ask you to provide sensitive information through a link.
Another thing that you can do to reinforce the security of your data is to keep an eye on the URLs of the sites you visit. Even if the site looks good and seems to be perfectly legitimate, the URL often gives the scammers away. Remember that sites that require a high level of security (such as online banking, payment processing methods and email services) normally use https instead of http.
Finally, you can get extra protection for your confidential data with the help of advanced programs like HijackThis and Process Monitor. These programs are designed to detect any spyware and tools that may be in place to capture your data. Another option to consider is to use a virtual machine/PC, which can make you less vulnerable to attacks.
Getting rid of Keyloggers
If you confirm the presence of a keylogger on your computer, you can follow the below steps to remove it:
- Open the task manager and select “end process” and select the suspicious program.
- Download a software removal tool. There are many good free options (PC Whiz is one of them) that will not only save you money, but can also keep your financial details secure as you will not need to compromise them by making a purchase while you are being monitored.
- Run the program and after the removal is complete, get anti-spyware protection from a reliable provider. Many fraudsters use false spyware detection software to lure their targets so it is important that you only choose a program from a recognized developer.
Keep in mind that in some cases, the spyware can be so persistent that you will require professional assistance to remove it. The best option is to take steps to prevent the issue instead of having to deal with it. Follow the tips mentioned above and you will be able to avoid spyware and reduce the risks to your sensitive information.